Track:
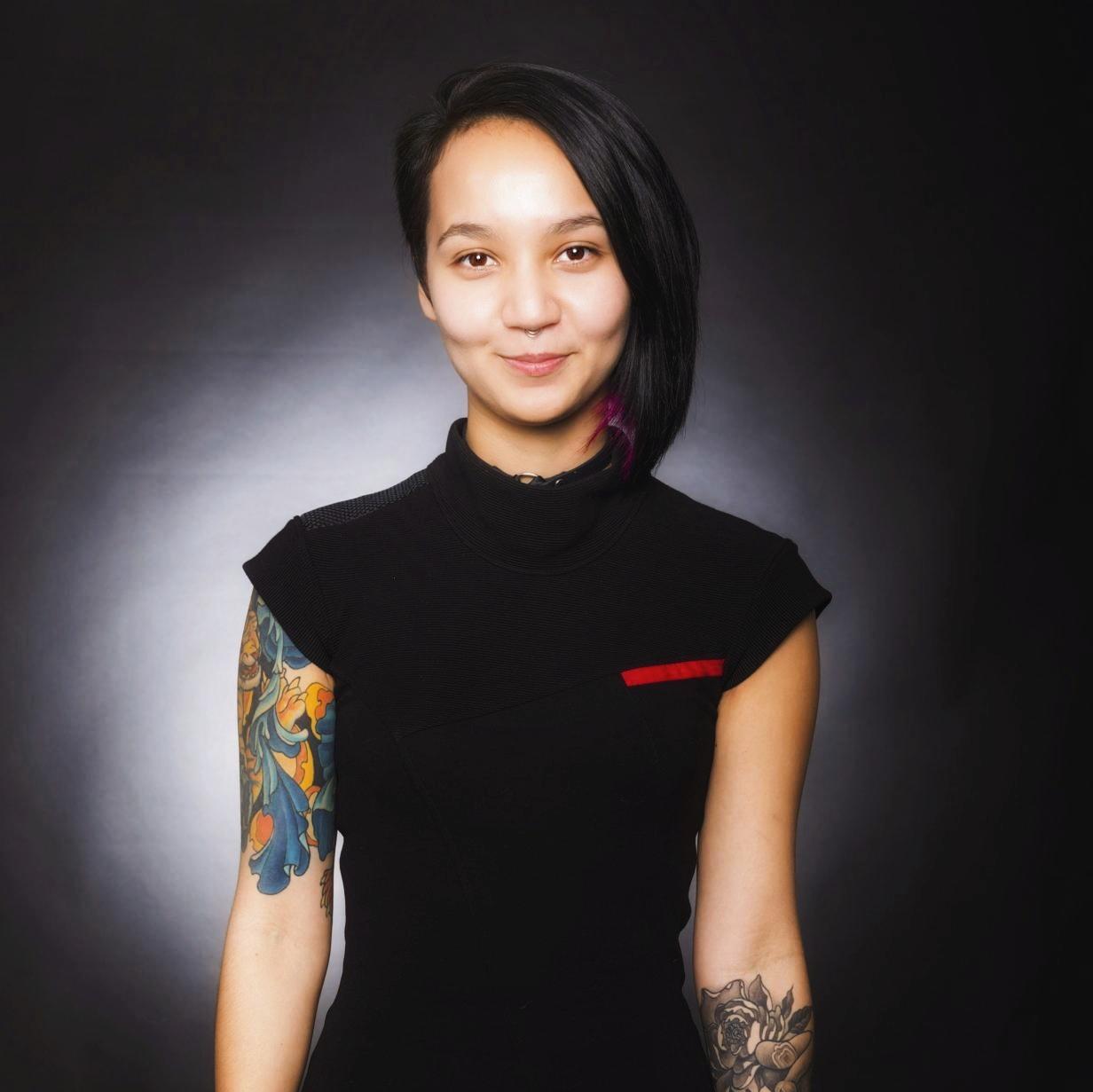
Security from the defender's AND the attacker's point of view
Christina Camilleri works on the infosec team at Riot Games where she focuses on improving security awareness training for Rioters, running awareness tests, and making use of data to inform on Rioter behaviors around security. Christina’s primary areas of expertise are web application penetration testing, open-source intelligence (OSINT), and social engineering -- not only the psychological and physical involvement of social engineering, but also the manipulation and social influencing techniques that are able to exploit (and help!) the behavior of others. Prior to joining Riot Games, Christina worked as a penetration tester at Bishop Fox, where she primarily concentrated her efforts in social engineering and web-application penetration testing. In her free time, Christina enjoys whiskey, Brazilian Jiu Jitsu and patting cats.
by Anastasiia Voitova
Security Enthusiast & Product Engineer @cossacklabs
In-depth technical inquiry about cryptography in a wider context: how it helps to narrow more significant risks to controlled attack surfaces, enables managing the risk efficiently and elegantly, how tools and algorithms sit in a broader context of managing infrastructure-wide risks associated with handling sensitive data.
Apart from discussing general technical approaches, we will focus on what do we need to do after we’ve implemented some kind of encryption in our system: monitoring...
by Laura Bell
Founder of SafeStack
Many people don't care about security. It's OK, don't worry! I'm not judging.
Security is the world of defense, of caution and of risk. Securing systems is hard and we don't have great solutions to the many challenges it poses. Security folk on the whole are the least exciting people to invite to your parties.
The time has come to change this.
So what if we...
by Emma McCall
Security Analyst @RiotGames
In this presentation we will analyze the EternalBlue exploit that was leaked in early 2017 which was then abused to great effect throughout the year.
Beginning a journey into InfoSec research can be daunting. We will discuss how targeted analysis can help develop security skills while still assisting company, clients and colleagues. Even when dealing with sophisticated exploits and malware in situations such as these.
by Marisa Fagan
Product Security Lead @Synopsys
As a Developer, there will come a time when you realize that you have the power to not only ship awesome features, but also protect them so that no one else can tamper with all your hard work. Every Developer is responsible for coding securely, but there are a brave few among us that will take this power one step further by wearing the mantle of a Security Champion.
This talk will be your guide to becoming the Security Champion...
by Michael Brunton-Spall
Independent Security Consultant, previously Deputy Director for Technology and Operation, & Head of CyberSecurity of Government Digital Service
Agile software development and security often don’t feel like good bedfellows. Many traditional security methodologies for analysing risk and threats are based on old military or government based software development methodologies which favour traditional, slow moving, low change systems.
Attack tree’s is a new way of understanding how your system might be attacked and how to prioritise security measures to be implemented. It makes it easy for product managers and technical...
Tracks
-
Microservices/ Serverless: Patterns and Practices
Stories of success and failure building modern service and function-based applications, including event sourcing, reactive, decomposition, & more.
-
Distributed Stateful Systems
Architecting and leveraging NoSQL revisitied
-
Evolving Java and the JVM: Mobile, Micro and Modular
Although the Java language is holding strong as a developer favourite, new languages and paradigms are being embraced on JVM.
-
The Practice & Frontiers of AI
Learn about machine learning in practice and on the horizon
-
Operating Systems: LinuxKit, Unikernels, & Beyond
Applied, practical, & real-world deep-dive into industry adoption of OS, containers and virtualisation, including Linux on Windows, LinuxKit, and Unikernels
-
Stream Processing in the Modern Age
Compelling applications of stream processing & recent advances in the field
-
Leading Edge Backend Languages
Code the future! How cutting-edge programming languages and their more-established forerunners can help solve today and tomorrow’s server-side technical problems.
-
Modern CS in the Real World
Applied trends in Computer Science that are likely to affect Software Engineers today.
-
DevEx: The Next Evolution of DevOps
Removing friction from the developer experience.
-
Bare Knuckle Performance
Killing latency and getting the most out of your hardware
-
Tech Ethics in Action
Learning from the experiences of real-world companies driving technology decisions from ethics as much as technology.
-
Security: Red XOR Blue Team
Security from the defender's AND the attacker's point of view
-
Architecting for Failure
If you're not architecting for failure you're heading for failure
-
Architectures You've Always Wondered About
Topics like next-gen architecture mixed with applied use cases found in today's large-scale systems, self-driving cars, network routing, scale, robotics, cloud deployments, and more.
-
Observability: Logging, Alerting and Tracing
Observability in modern large distributed computer systems
-
Speaker AMAs (Ask Me Anything)
-
Building Great Engineering Cultures & Organizations
Stories of cultural change in organizations
-
Speaker AMAs (Ask Me Anything)